Companies working with the U.S. Department of Defense must meet strict cybersecurity requirements to protect Controlled Unclassified Information (CUI). The Cybersecurity Maturity Model Certification (CMMC) framework establishes security standards that contractors must follow when handling sensitive government data.
One of the most common questions organizations ask is:
How much will CMMC compliance cost our company?
The answer depends on several factors including your environment, the number of systems in scope, and how your organization handles sensitive information.
This guide explains the primary factors that influence CMMC compliance costs and how contractors can estimate the potential investment required.
What Influences CMMC Compliance Cost?
CMMC implementation costs vary widely between organizations. The following factors typically determine the overall investment.
1. Size of the IT Environment
The number of devices and users that access systems handling sensitive data can significantly affect compliance scope.
Organizations with only a few endpoints will typically have a smaller implementation footprint, while larger networks require more extensive security controls and monitoring.
2. Whether You Use a Dedicated CUI Enclave
Some contractors isolate systems that process Controlled Unclassified Information into a dedicated secure environment known as a CUI enclave.
This approach limits the number of systems subject to compliance requirements, which can help reduce implementation complexity and cost.
3. Number of Systems Handling Sensitive Data
Servers, laptops, mobile devices, and specialized systems that interact with controlled data must be protected under CMMC requirements. The larger the protected environment, the greater the effort required to implement and maintain compliance.
4. Security Monitoring and Maintenance
CMMC compliance is not a one-time implementation. Organizations must maintain ongoing monitoring, logging, and security controls to remain compliant with the framework.
Continuous security operations, patch management, and incident response processes contribute to the long-term cost of compliance.
Why Many Contractors Misestimate CMMC Costs
Many organizations underestimate the effort required to implement and maintain CMMC controls.
Common challenges include:
expanding scope due to interconnected systems
unclear boundaries between compliant and non-compliant systems
lack of visibility into the number of devices handling sensitive data
Understanding your environment and defining the correct compliance scope is essential for estimating costs accurately.
Factors That Influence CMMC Compliance Cost
Organizations often assume there is a fixed price for CMMC compliance, but the cost varies depending on the scope and complexity of the environment. Understanding the key factors involved can help defense contractors estimate the level of effort required before planning implementation.
Below are four major elements that typically influence the investment required for CMMC compliance.
1. Environment Scope
CMMC compliance begins by defining which systems handle Controlled Unclassified Information (CUI). Devices, users, and servers that interact with this data must fall within the protected environment. The larger the scope, the greater the compliance effort.
2. Compliance Environment Type
Organizations may implement compliance through different architectures. Some isolate CUI systems within a secure enclave, while others apply controls across their broader network environment. The chosen architecture affects the number of systems subject to compliance.
3. Security Control Implementation
CMMC requires implementing security controls designed to protect defense-related information. These controls typically include identity management, system monitoring, endpoint protection, and security policy documentation.
4. Operational Monitoring & Maintenance
Compliance requires ongoing monitoring and system maintenance. Organizations must maintain logging, patch management, and security response processes to ensure continued readiness for assessments.
Estimating Your Organization’s CMMC Compliance Scope
Before planning implementation, contractors should first determine:
the number of devices handling CUI
the number of users accessing sensitive systems
whether a dedicated enclave is required
the level of security monitoring needed
Once these factors are defined, organizations can begin estimating the potential investment required for compliance.
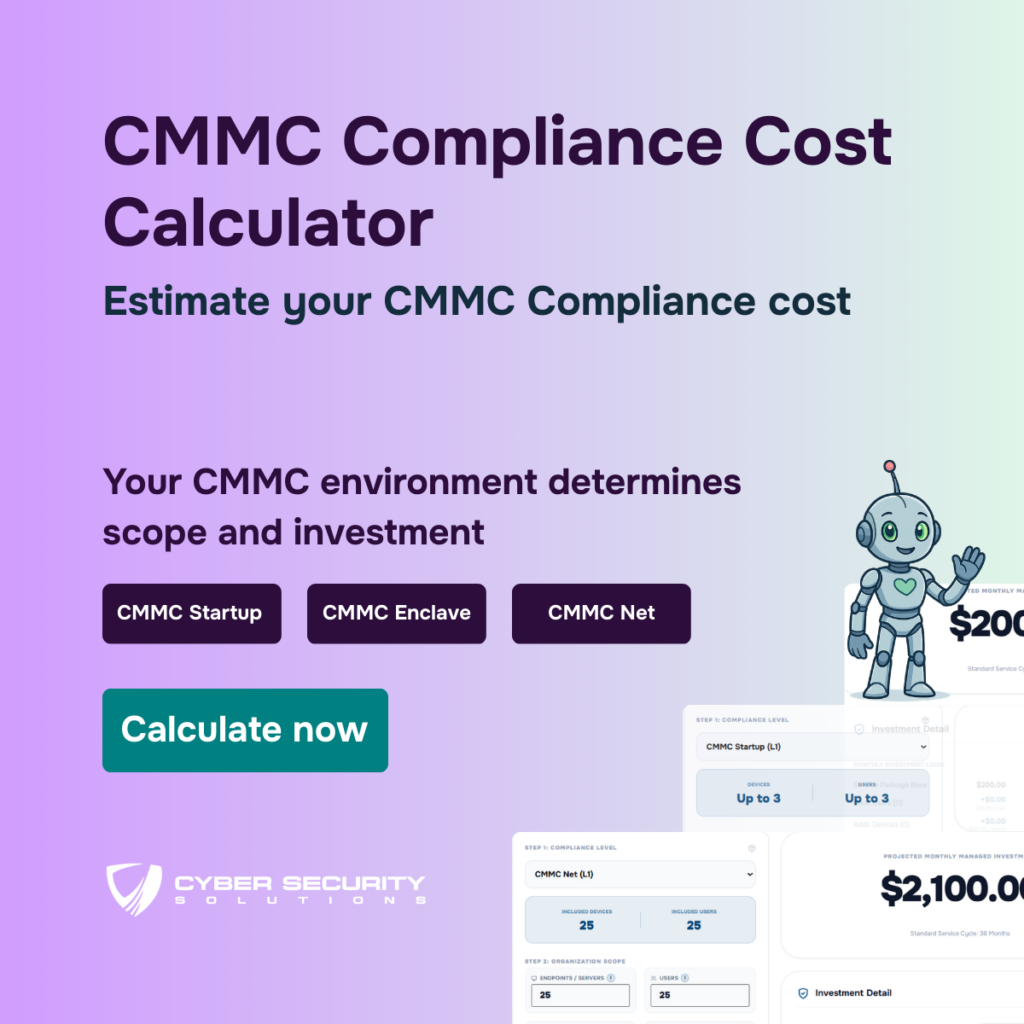
If you want a quick estimate based on your organization’s environment, you can use our interactive calculator to explore how different factors influence compliance investment.
It allows you to:
select your CMMC environment type
estimate based on number of devices and users
understand how scope impacts cost
Try the CMMC Compliance Cost Calculator
Once these factors are understood, organizations can begin estimating the potential scope of their CMMC compliance environment. Because every contractor’s infrastructure and operational model is different, having a simple way to explore how users, devices, and environment type affect compliance scope can be helpful during early planning.
To support this process, Cyber Security Solutions provides a calculator that allows organizations to explore different scenarios and better understand how these variables may influence their potential compliance investment.
Ready to close your business gaps?
Schedule a call with an expert.
Don’t worry, it’s free!
Author