
Compliance and Security Provided by Cyber Security Solutions
NIST SP 800-171 Rev 2 Assessment Package
CSS provides an evidence-based assessment that corelates vulnerabilities, risks, and compliance gaps into an actionable plan across our easy-to-read dashboards.
What all is Included?
- Full NIST/DFARS Compliance Assessment
- DoD Assessment Scorecard
- NIST SP 800-171/CMMC Compliance Scores
- Initial System Security Plan (SSP)
- Initial Plan of Actions & Milestones (POA&M)
- PIEE/SPRS Education & Assistance
What to know about
NIST SP 800-171 Rev 2
If your organization wants to do business with the Department of Defense (DoD), then NIST SP 800-171 Rev 2 should be at the top of your priority list. Under the new DFARS provision 252.204-7019 organizations are now required to implement NIST SP 800-171 standards and have a current DoD Assessment on record with results posted in the Supplier Performance Risk System (SPRS) in order to bid on DoD contracts.
Although claiming compliance with NIST SP 800-171 Rev 2 does not require a Third Party audit, it may be wise for your organization to work with an experienced partner to get an accurate assessment. Many organizations are having a difficult time properly accessing their environment and are relying on inaccurate results. Call today to learn why companies across North America are partnering with CSS for their NIST/DFARS assessment.
NIST SP 800-171 Rev 2
Documentation
We often talk about the documentation that is tied to a NIST SP 800-171 Rev 2 compliance assessment, but with all of the acronyms things can often get confusing. Take a look at the chart below to learn more about each of the NIST SP 800-171 documents that make up our assessment package.
Document
Purpose
CSS Provided
DoD Assessment Scorecard
(DoD Scorecard)
The DoD Scorecard is a one-For-One mapping of the assessment results to the NIST SP 800-171 Rev 2 requirements. The DoD Scorecard will provide the compliance score that your organization submits into SPRS.
System Security Plan
(SSP)
The SSP is the foundation of NIST SP 800-171 Rev 2 which describe system boundaries, operational environment, how requirements are implemented, and the relationships with/connections to other systems.
Plan of Action & Milestones
(POA&M)
The POA&M provides a description of why an organization is unable to satisfy a requirement, how the organization plans to address the gap, and a Remediation timeframe for correction.
Why Choose Cyber Security Solutions?
Our assessment process is not influenced by personnel involvement and extensive questionnaires. Results reported are actual configuration settings and documented evidence showing compliance or non-compliance. Your personnel will not have to answer hundreds of questions and attend countless meetings/calls that take weeks to complete.
Once results are compiled, we schedule an out brief to discuss all non-compliance findings with evidence. You will also receive a detailed report of findings along with the tools to plan out your compliance journey. We leverage our technology to ensure the most accurate results. Also, our package includes all of the necessary documentation to start your compliance journey at very affordable cost.
Expedited Process
Our process takes much less time than majority of our competitors.
The total time (from start to finish) is typically 1 week.
Time required from your personnel is generally less than 4 hours.
Accurate Results
We utilize our scanning agents to test the configurations and settings across your entire corporate network. This not only saves time and effort of going through lengthy questionaires, it ensures accuracy.
Thorough Out-briefing
Our out-briefing is in depth, where we spend the time to ensure your team understands your areas of non-compliance. We will also briefly cover your remediation path using our CMMC Compliance Dashboard.
call today to protect your business
Talk to one of our experts today to learn how we can identify your current risks and vulnerabilities and put together a package to better protect your.
NIST SP 800-171
Compliance Requirements.
Here is a look at the NIST SP 800-171 Rev 2 compliance requirements. Click on any of the 14 domains to view individual controls:
3.1.1 Limit information system access to authorized users, processes acting on behalf of authorized users, or devices (including other information systems).
3.1.2 Limit information system access to the types of transactions and functions that authorized users are permitted to execute.
3.1.3 Control the flow of CUI in accordance with approved authorizations.
3.1.4 Separate the duties of individuals to reduce the risk of malevolent activity without collusion.
3.1.5 Employ the principle of least privilege, including for specific security functions and privileged accounts.
3.1.6 Use non-privileged accounts or roles when accessing nonsecurity functions.
3.1.7 Prevent non-privileged users from executing privileged functions and audit the execution of such functions.
3.1.8 Limit unsuccessful logon attempts.
3.1.9 Provide privacy and security notices consistent with applicable CUI rules.
3.1.10 Use session lock with pattern-hiding displays to prevent access/viewing of data after period of inactivity.
3.1.11 Terminate (automatically) a user session after a defined condition.
3.1.12 Monitor and control remote access sessions.
3.1.13 Employ cryptographic mechanisms to protect the confidentiality of remote access sessions.
3.1.14 Route remote access via managed access control points.
3.1.15 Authorize remote execution of privileged commands and remote access to security-relevant information.
3.1.16 Authorize wireless access prior to allowing such connections.
3.1.17 Protect wireless access using authentication and encryption.
3.1.18 Control connection of mobile devices.
3.1.19 Encrypt CUI on mobile devices and mobile computing platforms.
3.1.20 Verify and control/limit connections to and use of external systems.
3.1.21 Limit use of portable storage devices on external systems.
3.1.22 Control CUI posted or processed on publicly accessible systems.
3.2.1 Ensure that managers, systems administrators, and users of organizational information systems are made aware of the security risks associated with their activities and of the applicable policies, standards, and procedures related to the security of organizational information systems.
3.2.2 Ensure that organizational personnel are adequately trained to carry out their assigned information security-related duties and responsibilities.
3.2.3 Provide security awareness training on recognizing and reporting potential indicators of insider threat.
3.3.1 Create, protect, and retain information system audit records to the extent needed to enable the monitoring, analysis, investigation, and reporting of unlawful, unauthorized, or inappropriate information system activity.
3.3.2 Ensure that the actions of individual information system users can be uniquely traced to those users so they can be held accountable for their actions.
3.3.3 Review and update audited events.
3.3.4 Alert in the event of an audit process failure.
3.3.5 Correlate audit review, analysis, and reporting processes for investigation and response to indications of inappropriate, suspicious, or unusual activity.
3.3.6 Provide audit reduction and report generation to support on-demand analysis and reporting.
3.3.7 Provide an information system capability that compares and synchronizes internal system clocks with an authoritative source to generate time stamps for audit records.
3.3.8 Protect audit information and audit tools from unauthorized access, modification, and deletion.
3.3.9 Limit management of audit functionality to a subset of privileged users.
3.4.1 Establish and maintain baseline configurations and inventories of organizational information systems (including hardware, software, firmware, and documentation) throughout the respective system development life cycles.
3.4.2 Establish and enforce security configuration settings for information technology products employed in organizational information systems.
3.4.3 Track, review, approve/disapprove, and audit changes to information systems.
3.4.4 Analyze the security impact of changes prior to implementation.
3.4.5 Define, document, approve, and enforce physical and logical access restrictions associated with changes to the information system.
3.4.6 Employ the principle of least functionality by configuring the information system to provide only essential capabilities.
3.4.7 Restrict, disable, and prevent the use of nonessential programs, functions, ports, protocols, and services.
3.4.8 Apply deny-by-exception (blacklist) policy to prevent the use of unauthorized software or deny-all, permit-by-exception (whitelisting) policy to allow the execution of authorized software.
3.4.9 Control and monitor user-installed software
3.5.1 Identify information system users, processes acting on behalf of users, or devices.
3.5.2 Authenticate (or verify) the identities of those users, processes, or devices, as a prerequisite to allowing access to organizational information systems.
3.5.3 Use multifactor authentication for local and network access to privileged accounts and for network access to non-privileged accounts.
3.5.4 Employ replay-resistant authentication mechanisms for network access to privileged and non-privileged accounts.
3.5.5 Prevent reuse of identifiers for a defined period.
3.5.6 Disable identifiers after a defined period of inactivity.
3.5.7 Enforce a minimum password complexity and change of characters when new passwords are created.
3.5.8 Prohibit password reuse for a specified number of generations.
3.5.9 Allow temporary password use for system logons with an immediate change to a permanent password.
3.5.10 Store and transmit only encrypted representation of passwords.
3.5.11 Obscure feedback of authentication information.
3.6.1 Establish an operational incident-handling capability for organizational information systems that includes adequate preparation, detection, analysis, containment, recovery, and user response activities.
3.6.2 Track, document, and report incidents to appropriate officials and/or authorities both internal and external to the organization.
3.6.3 Test the organizational incident response capability.
3.7.1 Perform maintenance on organizational information systems.
3.7.2 Provide effective controls on the tools, techniques, mechanisms, and personnel used to conduct information system maintenance.
3.7.3 Ensure equipment removed for off-site maintenance is sanitized of any CUI.
3.7.4 Check media containing diagnostic and test programs for malicious code before the media are used in the information system.
3.7.5 Require multifactor authentication to establish nonlocal maintenance sessions via external network connections and terminate such connections when nonlocal maintenance is complete.
3.7.6 Supervise the maintenance activities of maintenance personnel without required access authorization.
3.8.1 Protect (i.e., physically control and securely store) information system media containing CUI, both paper and digital.
3.8.2 Limit access to CUI on information system media to authorized users.
3.8.3 Sanitize or destroy information system media containing CUI before disposal or release for reuse.
3.8.4 Mark media with necessary CUI markings and distribution limitations.
3.8.5 Control access to media containing CUI and maintain accountability for media during transport outside of controlled areas.
3.8.6 Implement cryptographic mechanisms to protect the confidentiality of CUI stored on digital media during transport unless otherwise protected by alternative physical safeguards.
3.8.7 Control the use of removable media on information system components.
3.8.8 Prohibit the use of portable storage devices when such devices have no identifiable owner.
3.8.9 Protect the confidentiality of backup CUI at storage locations.
3.9.1 Screen individuals prior to authorizing access to information systems containing CUI.
3.9.2 Ensure that CUI and information systems containing CUI are protected during and after personnel actions such as terminations and transfers.
3.10.1 Limit physical access to organizational information systems, equipment, and the respective operating environments to authorized individuals.
3.10.2 Protect and monitor the physical facility and support infrastructure for those information systems.
3.10.3 Escort visitors and monitor visitor activity.
3.10.4 Maintain audit logs of physical access.
3.10.5 Control and manage physical access devices.
3.10.6 Enforce safeguarding measures for CUI at alternate work sites (e.g., telework sites).
3.11.1 Periodically assess the risk to organizational operations (including mission, functions, image, or reputation), organizational assets, and individuals, resulting from the operation of organizational information systems and the associated processing, storage, or transmission of CUI.
3.11.2 Scan for vulnerabilities in the information system and applications periodically and when new vulnerabilities affecting the system are identified.
3.11.3 Remediate vulnerabilities in accordance with assessments of risk.
3.12.1 Periodically assess the security controls in organizational information systems to determine if the controls are effective in their application.
3.12.2 Develop and implement plans of action designed to correct deficiencies and reduce or eliminate vulnerabilities in organizational information systems.
3.12.3 Monitor information system security controls on an ongoing basis to ensure the continued effectiveness of the controls.
3.12.4 Develop, document, and periodically update system security plans that describe system boundaries, system environments of operation, how security requirements are implemented, and the relationships with or connections to other systems.
3.13.1 Monitor, control, and protect organizational communications (i.e., information transmitted or received by organizational information systems) at the external boundaries and key internal boundaries of the information systems.
3.13.2 Employ architectural designs, software development techniques, and systems engineering principles that promote effective information security within organizational information systems.
3.13.3 Separate user functionality from information system management functionality.
3.13.4 Prevent unauthorized and unintended information transfer via shared system resources.
3.13.5 Implement subnetworks for publicly accessible system components that are physically or logically separated from internal networks.
3.13.6 Deny network communications traffic by default and allow network communications traffic by exception (i.e., deny all, permit by exception).
3.13.7 Prevent remote devices from simultaneously establishing non-remote connections with the information system and communicating via some other connection to resources in external networks.
3.13.8 Implement cryptographic mechanisms to prevent unauthorized disclosure of CUI during transmission unless otherwise protected by alternative physical safeguards.
3.13.9 Terminate network connections associated with communications sessions at the end of the sessions or after a defined period of inactivity.
3.13.10 Establish and manage cryptographic keys for cryptography employed in the information system.
3.13.11 Employ FIPS-validated cryptography when used to protect the confidentiality of CUI.
3.13.12 Prohibit remote activation of collaborative computing devices and provide indication of devices in use to users present at the device.
3.13.13 Control and monitor the use of mobile code.
3.13.14 Control and monitor the use of Voice over Internet Protocol (VoIP) technologies.
3.14.1 Identify, report, and correct information and information system flaws in a timely manner.
3.14.2 Provide protection from malicious code at appropriate locations within organizational information systems.
3.14.3 Monitor information system security alerts and advisories and take appropriate actions in response.
3.14.4 Update malicious code protection mechanisms when new releases are available.
3.14.5 Perform periodic scans of the information system and real-time scans of files from external sources as files are downloaded, opened, or executed.
3.14.6 Monitor the information system including inbound and outbound communications traffic, to detect attacks and indicators of potential attacks.
3.14.7 Identify unauthorized use of the information system.
Step 2:
Assessment Scanning
Our team will deploy agents to all devices used to access your corporate network.
Power settings need to be adjusted for the scan to run overnight, as a way to not impact operations.
Scans are typically started on Friday evening and
completed by Monday morning.
Results are compiled in our Secure Vault, housed in a FedRAMP approved environment.
Step 3:
Validate Results & Develop Reports
CSS personnel will verify scan results from all devices and generate your DoD Scorecard.
Your scores and results are uploaded into the Compliance and Monitoring Dashboard where the initial SSP and POA&M is developed.
An out-brief call is scheduled with your team to discuss results and potential remediation paths.
Step 4:
Delivery of Results & Out-Brief Call
During the scheduled out-brief call, details of the assessment scan and evidence are discussed.
Questions for required controls that could not be scanned will be discussed and documented.
CSS provides an overview and demonstration of the CMMC Compliance Dashboard, and discusses potential remediation plans to meet compliance.
Overview:
Final Deliverables
Full NIST/DFARS Compliance Assessment
DoD Assessment Scorecard
NIST SP 800-171/CMMC Compliance Scores
Initial System Security Plan (SSP)
Initial Plan of Actions & Milestones (POA&M)
PIEE/SPRS Education & Assistance
Step 1:
Project Kickoff
Once all documentation is complete (NDAs, contracts, etc.), we schedule a kickoff meeting to discuss the process and answer questions.
Information Request Forms help us identify all
devices that are in scope for the assessment.
The assessment is non-invasive, and we can assure data never leaves your network.
Our Process
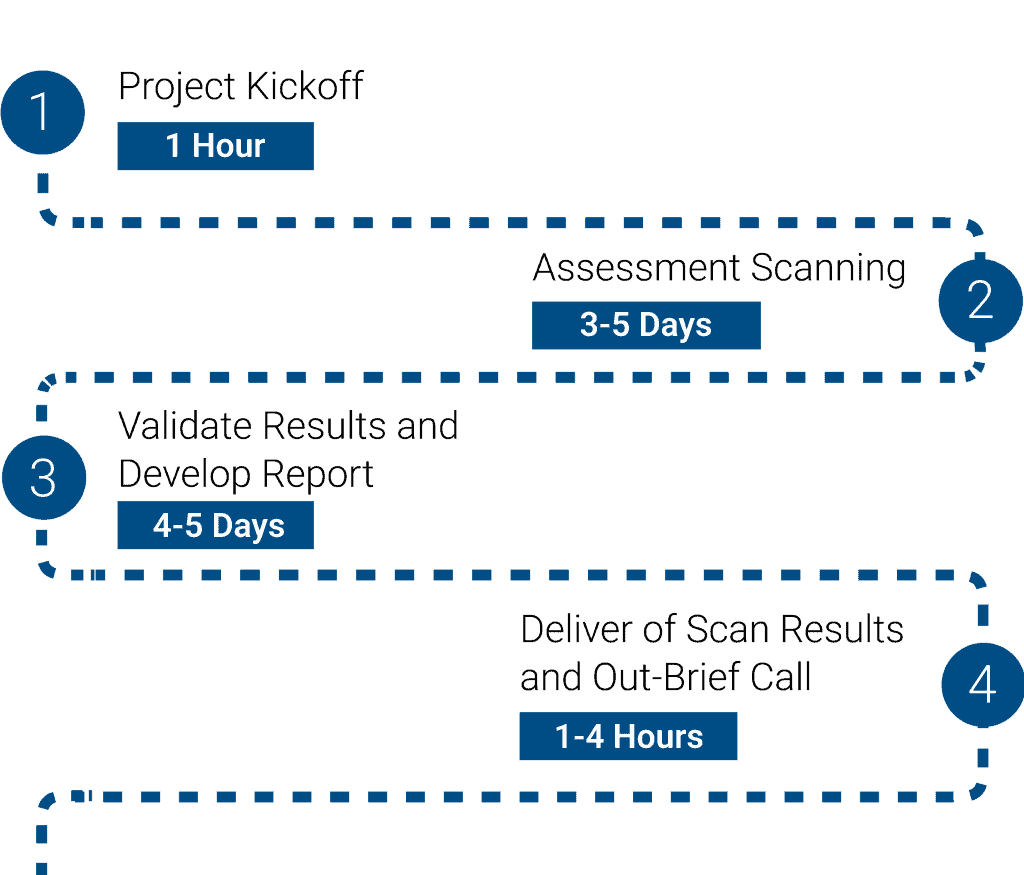
Our process starts with a project kickoff, where your team will work with our Onboarding Coordinator to provide access to your corporate devices. Our scanning agent is non-invasive, and your data never leaves your network. After we complete the scanning process we will validate all results and begin to develop your reports.
The out-briefing call is an in depth overview of everything that we found. This provides a deep understanding of the work ahead to implement NIST SP 800-171 Rev 2 requirements. The entire process typically takes 1 week from start to finish, and generally requires less than 4 hours of touch time from your personnel. Hover over each number on the flowchart to read more about our process.
Visual Process Roadmap
Just to make things a little bit easier to visualize, we wanted to show our roadmap for our NIST SP 800-171 Rev 2 assessment scan. Our team takes pride in being able to deliver results in a quick, detailed, and accurate manner.
Total Time (Start to Finish) is Typically 1 Week.
Time Required by Client's Team is Generally Less Than 4 Hours.
Give us a call today to gain a better understanding of your current vulnerabilities, risks, and compliance gaps!
Final Deliverables
• Full Compliance Assessment of Client's corporate environment
• DoD Assessment Scorecard & NIST SP 800-171/CMMC compliance scores
• Initial System Security Plan (SSP) & Plan of Actions & Milestones (POA&M)
• 1 year subscription to the CSS Compliance and Monitoring Dashboard
• Assistance/walkthrough (via Screen share) of submitting a score in PIEE/SPRS
Potential Remediation Services
In our cMMC Compliance Packages.
While these services are not included in our NIST SP 800-171 Assessment package, we do have CMMC Compliance packages that include everything your team will need to meet NIST/CMMC compliance. Click on any of the 30 services below to read more about what we provide as a part of our turn-key CMMC implementation packages:
We provide your full security hardware infrastructure through our Cyber Threat Compliance (CTC) platform. Our CTC includes everything from a compliant Firewall, IPS/IDS, Forward/Reverse Proxy, SIEM, and more.
Our Secure Vault platform offers a full cloud, filesharing, and collaboration tool located in our FedRAMP approved cloud environment. Our hybrid approach ensures maximum business uptime.
We develop your set of CMMC policies and procedures, reinforcing your organization’s security and compliance programs. We maintain them as requirements evolve, allowing you to focus on growing your business.
Our Compliance Dashboard provides leadership with a clear understanding of where your organization is along the compliance journey. Our documentation and reporting tools make C3PAO assessments a breeze.
Our team of expert Security Analyst are monitoring your corporate network around the clock to stop cybercriminals from infiltrating your network. CSS handle's all of the logging and reporting for you.
Can't connect to the printer? Email is down? Our experienced Help Desk team not only responds to client reported issues, but we often take care of issues before your team even notices.
We offer Security Awareness, Insider Threat, and Role Based User Access annual training modules to keep your team up to speed and within compliance. We also conduct phishing campaigns to keep your team ready.
Our Firewall as a Service provides the first layer of defense against all attacks. We handle the licensing, management, and security of our proprietary CTC platform where the firewall resides.
Our SIEM continuously monitors and acts upon real-time security information from virtually any source. We aggregate data from across your entire network, and analyze this data together to limit false-positives.
We provide all users with Multi-Factor Authentication (MFA) to ensure that the process of signing into your corporate systems is secure. We add in the benefit of Single Sign-On (SSO) to simplify your daily workflow.
We complete a full compliance assessment of your organization to measure gaps in NIST SP 800-171 and CMMC requirements. Results are imported into our Compliance Dashboard for live progress tracking.
The worst type of risks are the ones that have yet to be
identified/addressed. We work with you to understand the current state of your security posture and explain the business or financial impact of associated risks.
Our Exposure Assessment monitors external communications to your infrastructure and compares the detected communications and attempted attacks with vulnerabilities detected in our Vulnerability Scan.
Our vulnerability scan illuminates the unknown. We leave no stone left unturned; this scan enables the detection of devices, services, and vulnerabilities that were running without the knowledge of your team.
Our secure storage solution is security enforced, SOC monitored, and Disaster Recovery supported. Our team will perform automated synchronization through scheduled or continuous backups, that fit your needs.
Our Secure Backup service provides desktops with a means of file protection from natural disaster and ransomware. We ensure that your company's most important types of files are not lost in an incident.
Our Email Filtering ensures everyone operates in a secure/compliant manner. We protect you from malware and spam, as well as advanced threats like targeted spear phishing and ransomware.
Our Web Security service can be used to limit use of certain websites or block them entirely on corporate networks. This adds a layer of defense to your data by preventing the clicking of known malicious links.
Our Data Encryption service provides necessary device level data protection for security and compliance. We ensure your data remains secure and reduce the change of interception by unauthorized viewers.
Patching is a standard and well known requirement that many IT companies offer for an additional fee. We don't charge anything extra to provide this necessity since it's a compliance requirement and good practice.
Anti-Virus/Anti-Malware from CSS will always ensure that the latest attack prevention methods are in place on all endpoints, while managing any and all vendors required to provide the security.
Our VPN solution enables company owned devices to access internal network services from remote locations. A trustworthy VPN will secure and encrypt your internet, keeping data safe from malicious eyes.
Our Disaster Recovery service provides a means of file restoral and services on protected servers. We provide a complete service restoral in our cloud in as little as 4 hours, even if complete server hardware loss occurs.
Incident Response provides a team of experts in response to cyber incidents as required by regulatory compliance. We quickly determine the source, cause and extent of a breach, to include proper reporting.
Every incident is investigated and categorized, executed, and notified; all while being tracked using our After Actions Reports. Our After Actions Report is used to prove compliance requirements.
Our Reporting Platform enables decision makers to to help make cost saving decisions. Managers can prioritize replacement of the most troublesome equipment and increase workforce productivity.
Data Destruction is required for compliant disposal of assets that once held CUI. We ensure that your data storage assets are properly wiped using standards that meet or exceed your regulatory compliance needs.
Our Remote Workforce Tool allows employees to work securely from anywhere as if they were sitting at their desk. This provides the most secure means of accessing devices from anywhere in the world.
Our Secure Chat provides employees in the office, or working remote through web application or phone app, to chat in a secure and compliant manner. Chat is a client favorite for direct and team communications.
Our team installs Microsoft Office and provides licenses to every endpoint that we protect. Everyone is familiar with Microsoft products, which is why we provide cost savings for a tool you use the most.
Additional Resources
Our team has put together a list of resources and helpful links to provide a deeper understanding as you look to understand your NIST SP 800-171/DFARS compliance status. Click on the links to download some of our additional materials or visit the applicable website to learn more. You can also click below to talk to one of our experienced team members to hear more about our packaged offerings.
Resource Title
Attribution
Resource Link
Resources
